April 14, 2026
| CYBERSECURITY | ⏱ 10 min read | 📅 April 2026 | ✍ Carl Williams, NzingaNet Inc. |
Nearly half of all cyberattacks now target small and mid-sized businesses.
Let that sink in.
While the headlines focus on mega-breaches at huge companies, there's a quiet, devastating problem happening every day to organizations just like yours.
Small and mid-sized companies are getting hit hard, costing many of them hundreds of thousands to millions in lost money, damaging their reputation, and forcing them into tough recovery efforts. It's a real epidemic, and it's far more common than most people realize.
So what cybersecurity mistakes are putting SMBs at risk, and how do you fix them before they cost you?
In this guide, we'll explain the top 5 mistakes SMBs often make. More importantly, we'll show you exactly how you can avoid them.
TABLE OF CONTENTS
- What Is Cybersecurity and Why Does It Matter for SMBs?
- Why Are SMBs Being Targeted More Than Ever?
- How Do You Know If Your Business Is Already at Risk?
- The 5 Cybersecurity Mistakes SMBs Can't Afford to Make
- Mistake 1: Not Taking Backup & Disaster Recovery Seriously
- Mistake 2: Believing "We're Too Small to Be Targeted"
- Mistake 3: Using Weak Passwords and Skipping MFA
- Mistake 4: Delaying Software Updates and Security Patches
- Mistake 5: Dismissing Managed Security as "Too Expensive"
- You Don't Have to Figure This Out Alone
- FAQs
THE BASICS
What Is Cybersecurity and Why Does It Matter for SMBs?
Most small business owners hear the word "cybersecurity" and picture some IT guy in a dark room staring at lines of code. That's not what it is.
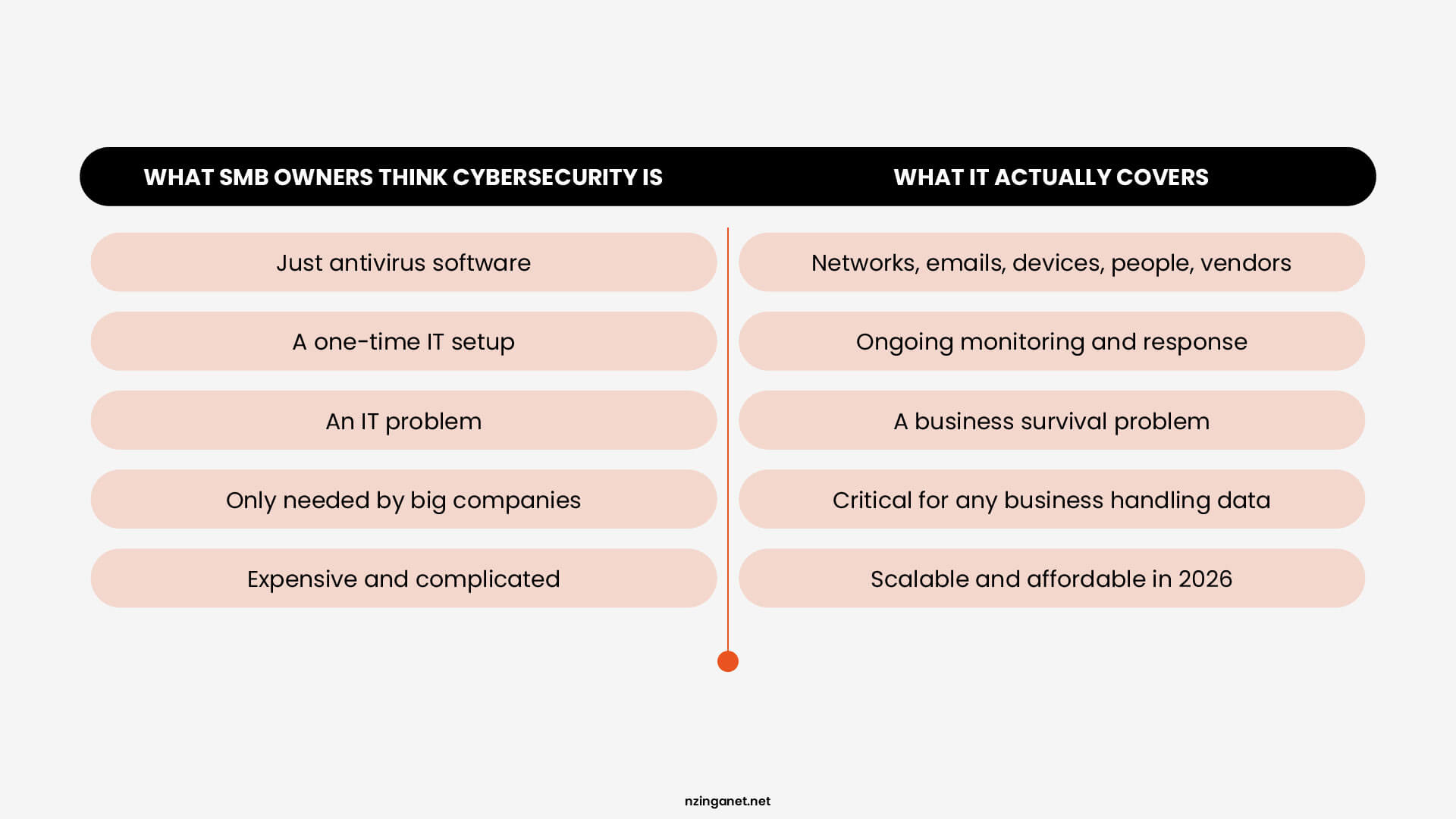
Cybersecurity is simply protecting your business from people who want to steal from you, shut you down, or hold your data hostage. And the targets aren't just big banks or tech companies anymore.
If your business has:
- Customer records
- Payment information
- Employee data
- Business emails
- Any cloud software
Then you have something worth stealing.
The problem is that most SMB owners think of cybersecurity as a one-time setup. Install antivirus, set a password, done. But that's like locking your front door and leaving every window wide open.
THREAT LANDSCAPE
Why Are SMBs Being Targeted More Than Ever?
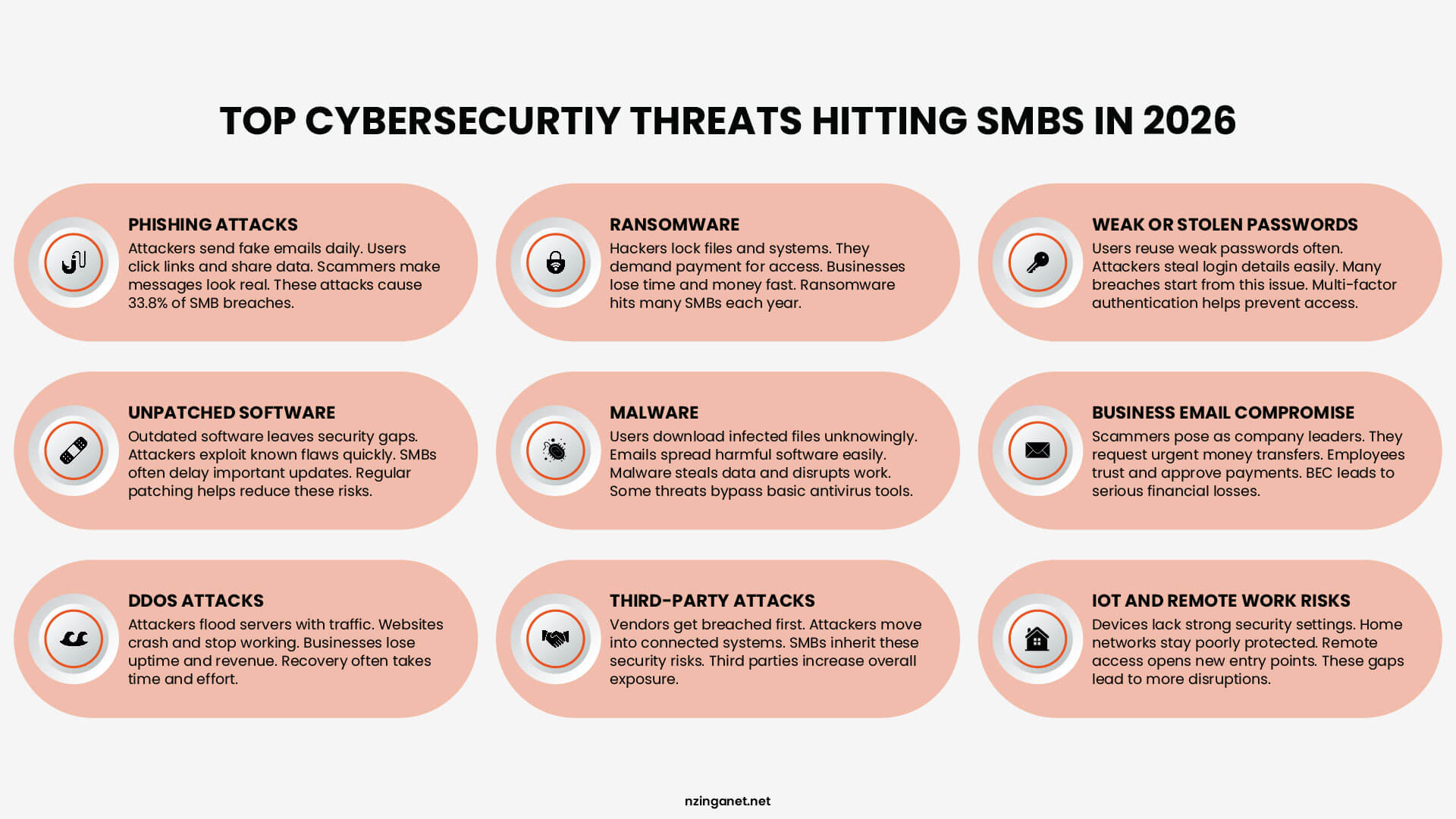
There's a myth that hackers only go after big companies because that's where the money is. That used to be partially true. But it hasn't been accurate for years.
Today, attacking a large enterprise is expensive and difficult. They have full security teams, advanced tools, and serious budgets. Breaking through takes real effort, and the risk of getting caught is high.
Attacking a small business? Much easier. And there are millions of them.
Cybercriminals think like business people. They want the best return on their effort. And small businesses consistently offer weak defenses, valuable data, and a high chance of paying up when things go wrong.
SELF-ASSESSMENT
How Do You Know If Your Business Is Already at Risk?
Before we get into the mistakes, it helps to know where you actually stand right now.
Go through this checklist honestly. No one's grading you. But your answers will tell you a lot about how exposed your business really is.
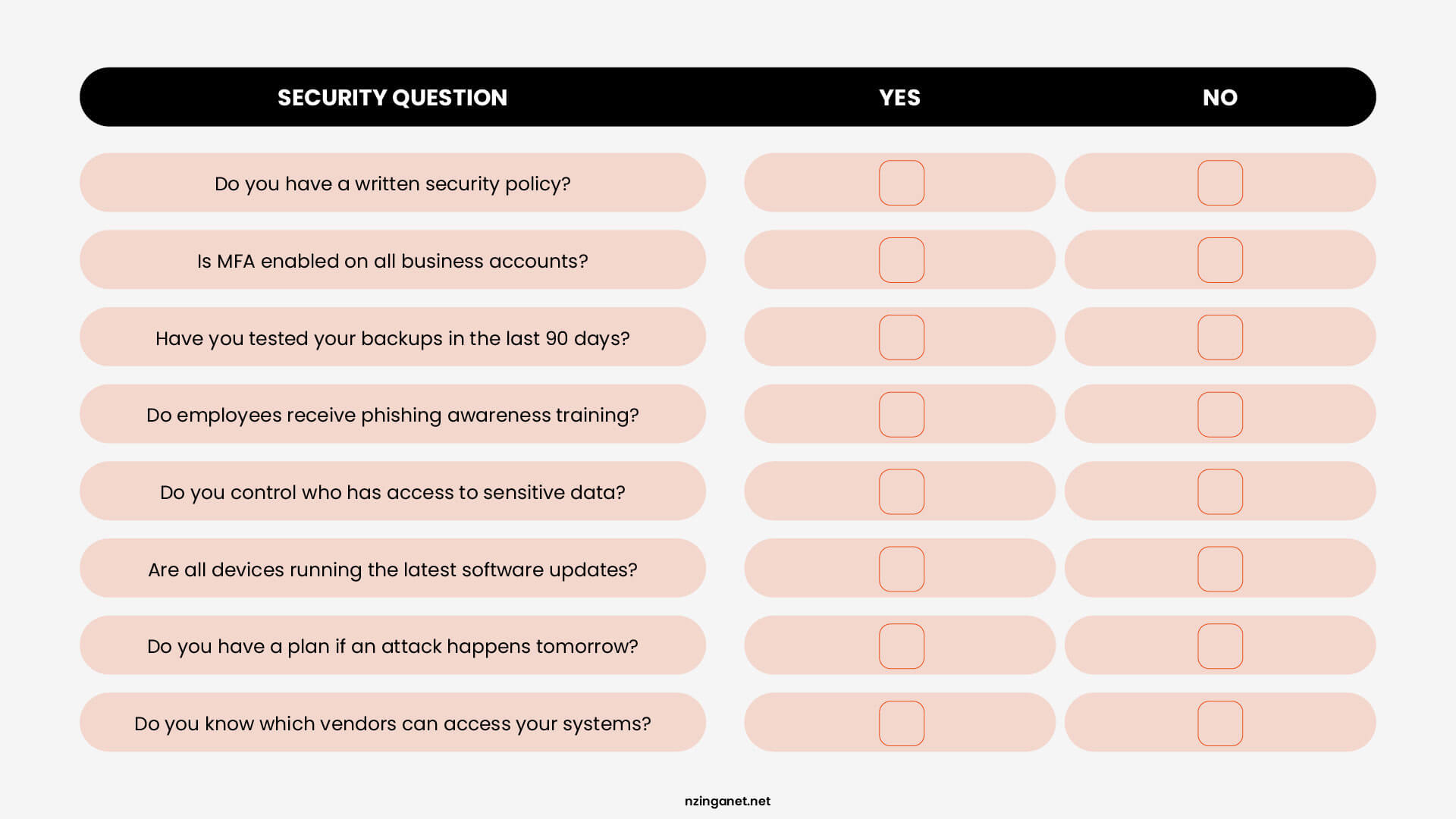
What your score means:
|
7–8 YES You're in decent shape. Focus on maintaining what you have and closing any remaining gaps. |
4–6 YES You have real exposure. Some quick fixes can make a big difference fast. |
0–3 YES Your business is at serious risk right now. The mistakes below apply directly to you. |
Most SMBs land in that middle range. They've done some things right but left enough gaps that a motivated attacker could find a way in. If you answered no to more than three of these, keep reading. The next section explains exactly what's going wrong and how to fix it.
THE CORE ISSUES
The 5 Cybersecurity Mistakes SMBs Can't Afford to Make
MISTAKE #1
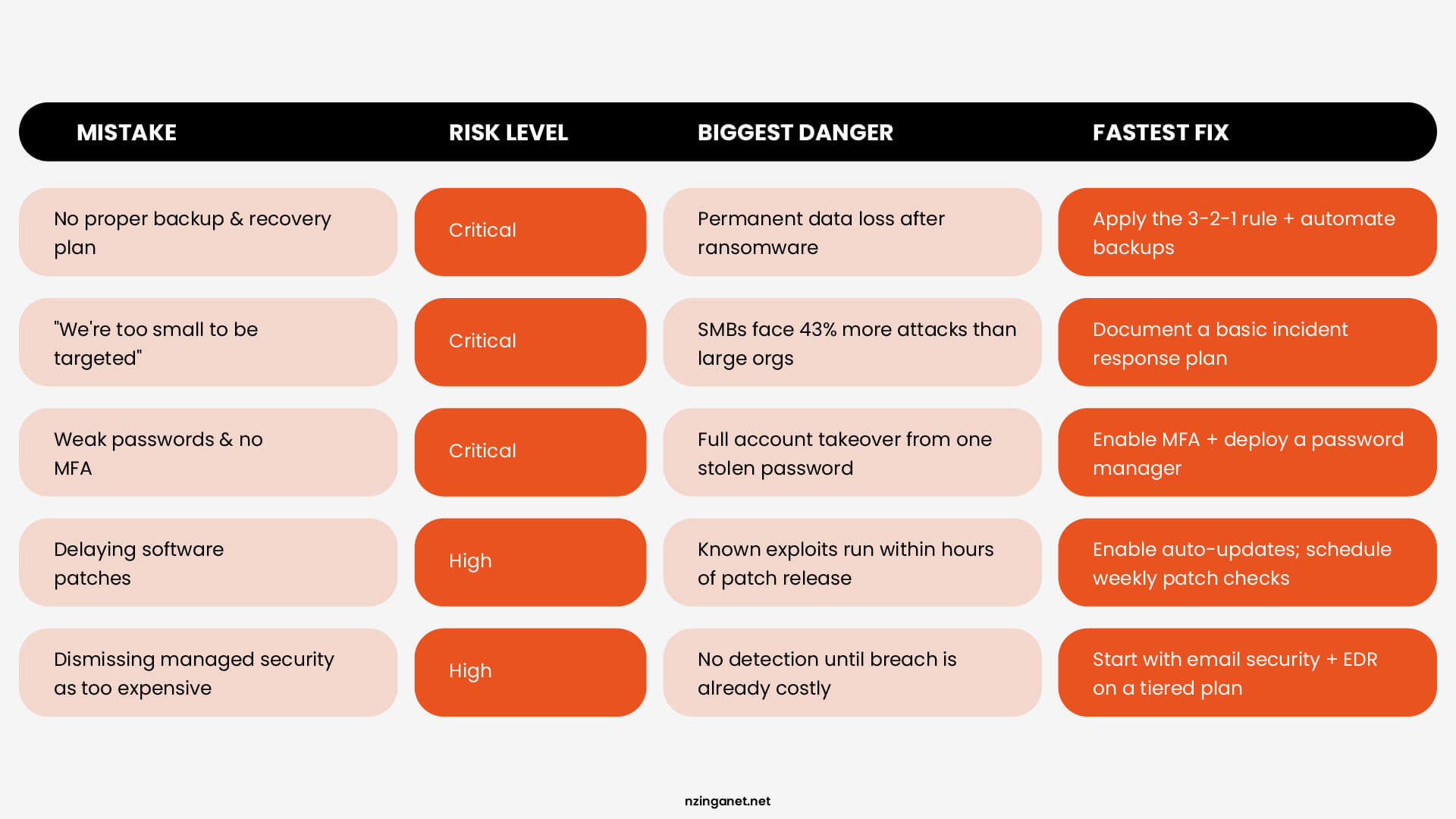
Not Taking Backup and Disaster Recovery Seriously Enough
Many small business owners assume that saving files to Google Drive or Dropbox counts as a disaster recovery plan. It doesn't and that assumption has cost businesses weeks of downtime and permanent data loss.
Without proper backup and disaster recovery strategies, mid-market companies face average recovery costs exceeding $1.5 million per incident. Ransomware attacks on small businesses have increased by 41% year-over-year, and attackers specifically target businesses with weak or nonexistent backups because those owners are far more likely to pay up.
How to Fix It
|
||
|
||
|
||
|
MISTAKE #2
Believing "We're Too Small to Be Targeted"
This is one of the most common cybersecurity mistakes small business owners make, and it is also the most dangerous because it stops any protective action before it starts.
Cybercriminals love under-defended, small and midsize businesses because they offer the perfect risk-reward ratio. Unlike large corporations with dedicated security teams and unlimited budgets, or organizations with minimal valuable data, SMBs represent high-value targets with predictably weak defenses.
The statistics support this targeting strategy. Small businesses experience 43% more cyber attacks but deploy 31% fewer security controls than larger organizations. This gap creates opportunities that professional cybercriminals exploit systematically across entire industries.
How to Fix It
|
||
|
||
|
||
|
MISTAKE #3
Using Weak Passwords and Skipping Multi-Factor Authentication (MFA)
Weak credentials rank among the most avoidable cybersecurity mistakes. Password habits that worked for a two-person team become serious vulnerabilities as the business grows.
These practices create credential-based vulnerabilities that attackers can exploit through password spraying, credential stuffing, or social engineering attacks.
And without Multi-Factor Authentication (MFA), a stolen password is all it takes to get full access to your email, accounting software, or customer data. Your business email is an especially high-value target, as it contains everything an attacker needs to impersonate you, defraud customers, or move deeper into your systems.
How to Fix It
|
||
|
||
|
||
|
MISTAKE #4
Delaying Software Updates and Security Patches
We get it — updates pop up at inconvenient times and sometimes feel like they break more than they fix. But delaying patches is one of the most preventable cybersecurity mistakes an SMB can make.
When a vulnerability is discovered in software, attackers start scanning for businesses running outdated versions almost immediately. Automated tools can identify and exploit these weaknesses across thousands of targets within hours of a patch being released. If you're running old software, you're essentially leaving a known unlocked door in plain sight.
One unpatched application or device can give attackers a foothold to move through your entire network even if everything else is up to date.
How to Fix It
|
||
|
||
|
||
|
MISTAKE #5
Dismissing Managed Security as "Too Expensive"
Dismissing managed security as too expensive is a cybersecurity mistake that tends to be the most expensive one on this list once a breach actually happens. When budgets are tight, cybersecurity often gets treated as a luxury rather than a necessity.
What many SMB owners don't realize is that managed security has evolved. You no longer need a full in-house IT team, enterprise-grade infrastructure, or a six-figure budget to get serious protection. Today's managed security service providers (MSSPs) offer scalable, subscription-based models designed specifically for organizations like yours.
How To Fix It
|
||
|
||
|
||
|
TAKE ACTION
You Don't Have to Figure This Out Alone
If reading through these cybersecurity mistakes made you realize your business has some gaps, that is a good thing. Awareness is the first step. The second step is talking to someone who can help you see exactly where you stand.
At NzingaNet, we work with small and mid-sized businesses every day to build practical, right-sized cybersecurity strategies that actually fit your budget and your reality.
If you'd like a clearer picture of your current security posture, we'd love to have a conversation.
| Schedule a Free Consultation → |
COMMON QUESTIONS
Frequently Asked Questions
PENNSYLVANIA & BEYOND
Stop Cybersecurity Mistakes Before They Cost You — NzingaNet Can Help
NzingaNet provides managed IT and cybersecurity services to small and mid-sized businesses across Pennsylvania and the surrounding region. From endpoint protection to compliance readiness, we handle the security so you can focus on your business.
| Explore Managed IT Services | Schedule a Free Consultation |



