May 11, 2026
| CYBERSECURITY | ⏱ 10 min read | 📅 May 2026 | ✍ Carl Williams, NzingaNet Inc. |
Imagine a cloud giant like Oracle, with world-class security, still losing 6 million records across 140,000 tenants in early 2025. A threat actor exploited an unpatched vulnerability in legacy Access Manager systems (CVE-2021-35587 from the January 2022 Critical Patch Update), triggering what researchers called a major supply chain attack.
Oracle denied the breach, but verified data samples hit dark web forums like BreachForums after ransom talks failed, proving even top-tier defenses can't protect blind spots in your attack surface.
These hidden gaps in visibility are exactly what Attack Surface Management (ASM) seeks to identify and secure, helping organizations stay ahead of threats before they can be exploited.
TABLE OF CONTENTS
- Key Takeaways
- What Is Attack Surface Management?
- What Does Attack Surface Management Include?
- Attack Surface vs. Threat Surface: What's the Difference?
- What Are the Different Types of Attack Surfaces?
- Attack Surface Management vs Vulnerability Management
- What Is the Attack Surface Management Process?
- Best Attack Surface Management Tools in 2026
- What Should You Look for in an ASM Platform?
- Attack Surface Management Best Practices
- Frequently Asked Questions

QUICK SUMMARY
Key Takeaways
- Attack surface management (ASM) is the continuous process of discovering, monitoring, and reducing all the digital entry points an attacker could use to reach your systems.
- Every connected asset is part of your attack surface: websites, cloud storage, employee devices, APIs, vendor portals, and even LinkedIn profiles that reveal your tech stack.
- The global ASM market reached $1.25 billion in 2026 and is projected to grow to $5 billion by 2034, driven by cloud adoption, remote work, and increasingly automated attack infrastructure.
- ASM and vulnerability management are not the same. ASM discovers what exists and who can reach it. Vulnerability management identifies weaknesses in what you already know you have.
- Continuous ASM outperforms periodic scanning because attack surfaces change every day. New cloud assets, new employees, new vendor integrations all expand what attackers can see.
DEFINITION
What Is Attack Surface Management?
Attack Surface Management (ASM) is a continuous, structured process for identifying and securing every digital asset an organization owns or uses that could be reached by an attacker. It involves discovering assets, assessing the risk each one poses, monitoring them for changes or new exposures, and taking action to reduce the risks they create.
Understanding your attack surface means knowing every entry point a hacker could use to access your systems. Each entry point represents a potential pathway to your data, applications, or network.
The average breach goes undetected for 181 days, according to SonicWall's 2026 Cyber Protect Report. This long detection window reflects not the sophistication of attackers, but a lack of visibility on the defender's side. ASM directly addresses this visibility gap, helping organizations find and secure vulnerable assets before attackers can exploit them.
SCOPE
What Does Attack Surface Management Include?
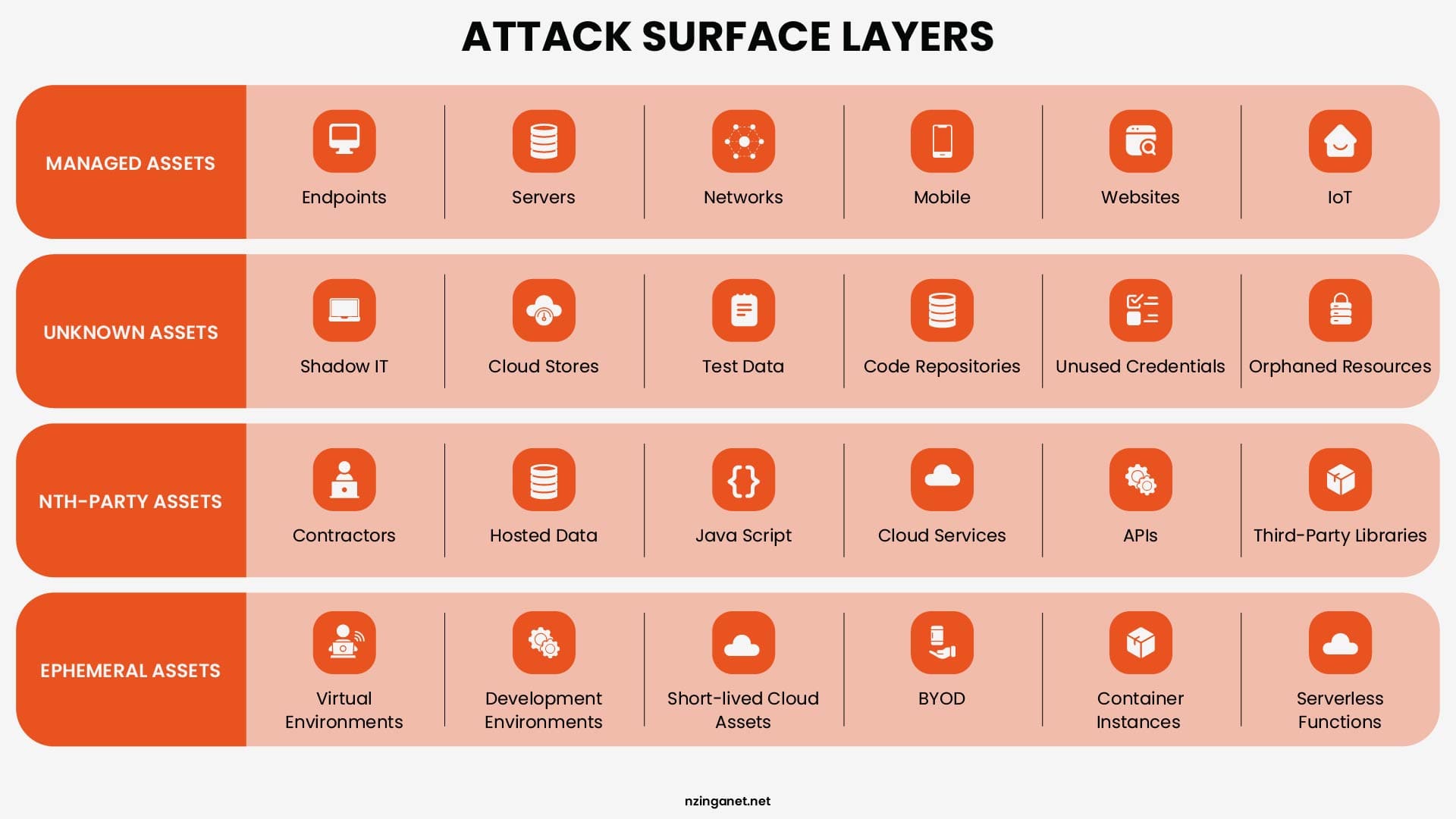
ASM covers the full lifecycle of external digital asset management, from initial discovery through ongoing monitoring. It starts by finding every asset that exists, be it known systems in your inventory, shadow IT that exists without formal approval, forgotten infrastructure from past projects, assets inherited through acquisitions, and the digital footprints of third-party vendors who have access to your systems.
Key components of the attack surface management include:
- Websites and web applications that customers and employees use
- Cloud services like storage accounts, databases, and email systems
- Employee devices including laptops, phones, and tablets
- Network connections such as VPNs and remote access tools
- APIs and integrations that connect different software systems
- Old servers or forgotten systems that still run in your environment
According to the NIST Cybersecurity Framework's 'Identify' function, organizations must first create a complete inventory of digital assets before they can protect them effectively. Asset identification is the foundation of attack surface management, because when leadership knows exactly what systems exist, they can allocate resources and security investments to the highest‑risk areas.
CONCEPT CLARIFICATION
Attack Surface vs. Threat Surface: What's the Difference?
An attack surface is the sum of all exposed, tangible entry points (software, hardware, network) an attacker can use to enter a system, while the threat surface is a broader, strategic concept encompassing all potential risks, vulnerabilities, and threat actors that could exploit those entry points. Essentially, the attack surface is "where" you can be attacked, and the threat surface is "how" or "what" could attack you.
| Aspect | Attack Surface | Threat Surface |
|---|---|---|
| Definition | All exploitable entry points and assets | All possible threats, actors, and attack methods |
| Focus | Technical exposure | Risk context and adversarial behavior |
| Scope | Narrower, asset-based | Broader, includes intent and capability |
| Key Question | "Where can we be attacked?" | "Who might attack, how, and why?" |
| Nature | Quantifiable and controllable | Dynamic and intelligence-driven |
While the attack surface shows you where you are exposed, the threat surface helps you understand which exposures are most likely to be exploited. Together, these concepts allow organizations to:
- Prioritize security efforts on high-risk areas
- Implement proactive controls to reduce both exposure and threat likelihood
- Allocate resources efficiently to protect the most critical assets
CLASSIFICATION
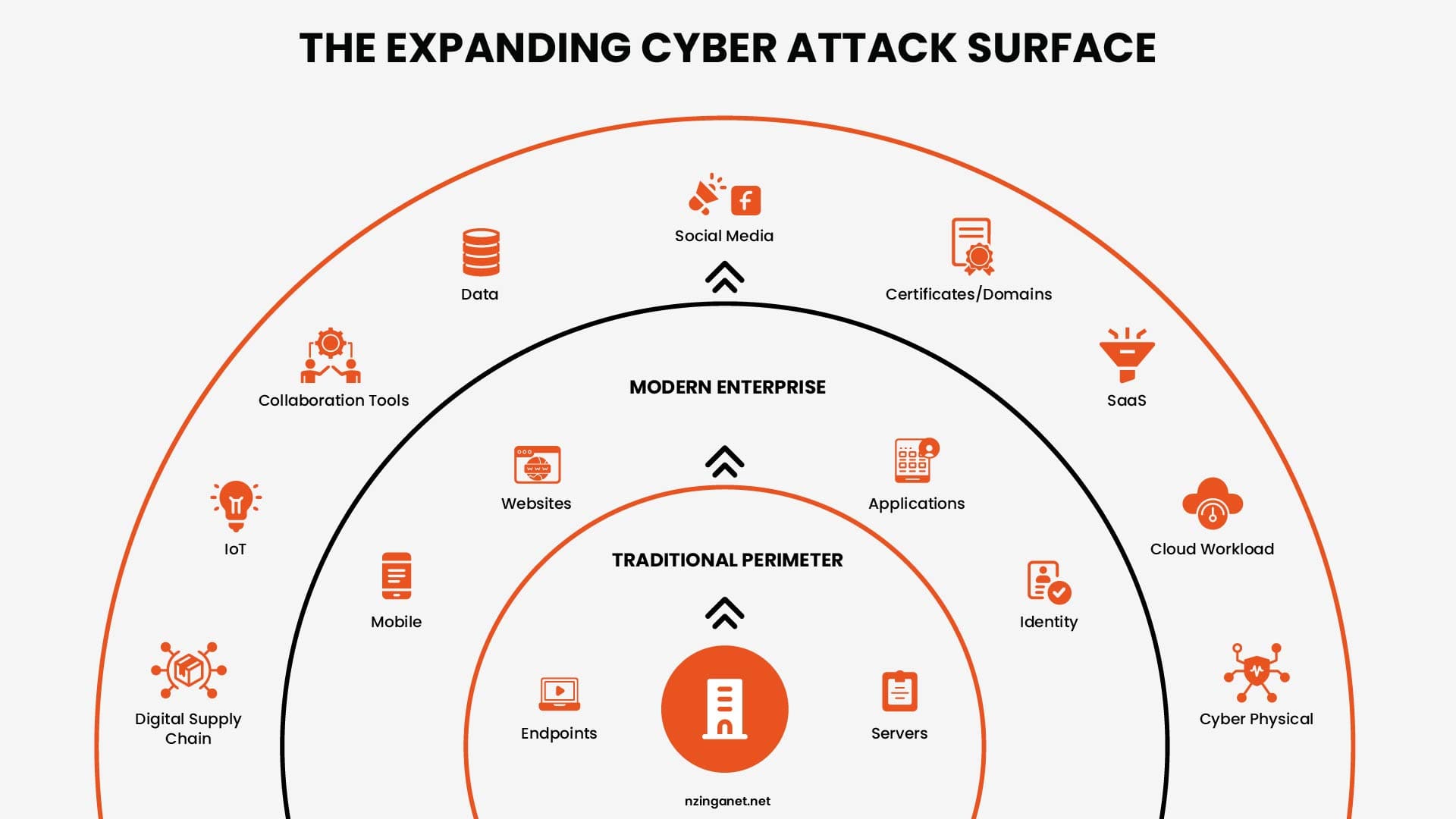
What Are the Different Types of Attack Surfaces?
An attack surface is any point where an organization's systems, networks, applications, or people can be exposed to cybersecurity threats. Understanding each type of attack surface helps identify vulnerabilities and improve overall security posture.
| Type | Common Exposures |
|---|---|
| Digital | Open ports, misconfigured cloud buckets, expired certificates, exposed admin panels, indexed API keys |
| Cloud | Public-access storage, overpermissioned service accounts, misconfigured security groups, unencrypted data at rest |
| Network | Default credentials, unpatched firmware, unencrypted services, overly permissive firewall rules |
| Application | Injection vulnerabilities, outdated libraries, weak authentication, hardcoded secrets in source code |
| Social | Phishing targets, credential reuse, social engineering vectors, publicly visible security team names |
| Supply Chain | Compromised dependencies, vendor credential reuse, overly permissive third-party API access |
| Physical | Unlocked device access, unencrypted USB drives, tailgating vulnerabilities, unmonitored device connections |
COMPARISON
Attack Surface Management vs Vulnerability Management: What Is the Difference?
Attack Surface Management (ASM) focuses on discovering and minimizing all external, internet-facing assets to reduce potential entry points, while Vulnerability Management (VM) focuses on identifying, assessing, and patching known security flaws within internal and external systems.
| Dimension | Attack Surface Management | Vulnerability Management |
|---|---|---|
| Primary question | What assets do we have and who can see them? | What weaknesses exist in our known assets? |
| Scope | All assets: known, unknown, shadow IT, third-party | Known, inventoried assets only |
| Discovery method | Outside-in, attacker's perspective | Inside-out, scanner-based |
| Monitoring cadence | Continuous, real-time | Periodic, scheduled scans |
| What it finds | Unknown assets, exposed services, misconfigurations, risky access points | CVEs, outdated software, configuration flaws in known systems |
| Third-party coverage | Yes, including supplier and vendor exposure | Limited, typically internal systems only |
| Primary output | Asset inventory, risk-scored exposure map | Vulnerability report with severity rankings |
| Primary action | Reduce and monitor the attack surface | Patch and remediate identified vulnerabilities |
| Best analogy | Mapping every door, window, and entrance to a building | Checking the locks on doors you already know about |
Censys research found that up to 80% of an organization's attack surface may be unknown to security teams. That means vulnerability management, on its own, leaves a massive blind spot.
Most security researchers consistently recommend treating vulnerability management as a function that operates on the asset inventory that ASM provides, rather than treating either discipline as sufficient on its own.
PROCESS
What Is the Attack Surface Management Process?
ASM is a continuous operational cycle with four distinct phases. Each phase feeds into the next, and the process repeats as the attack surface changes.
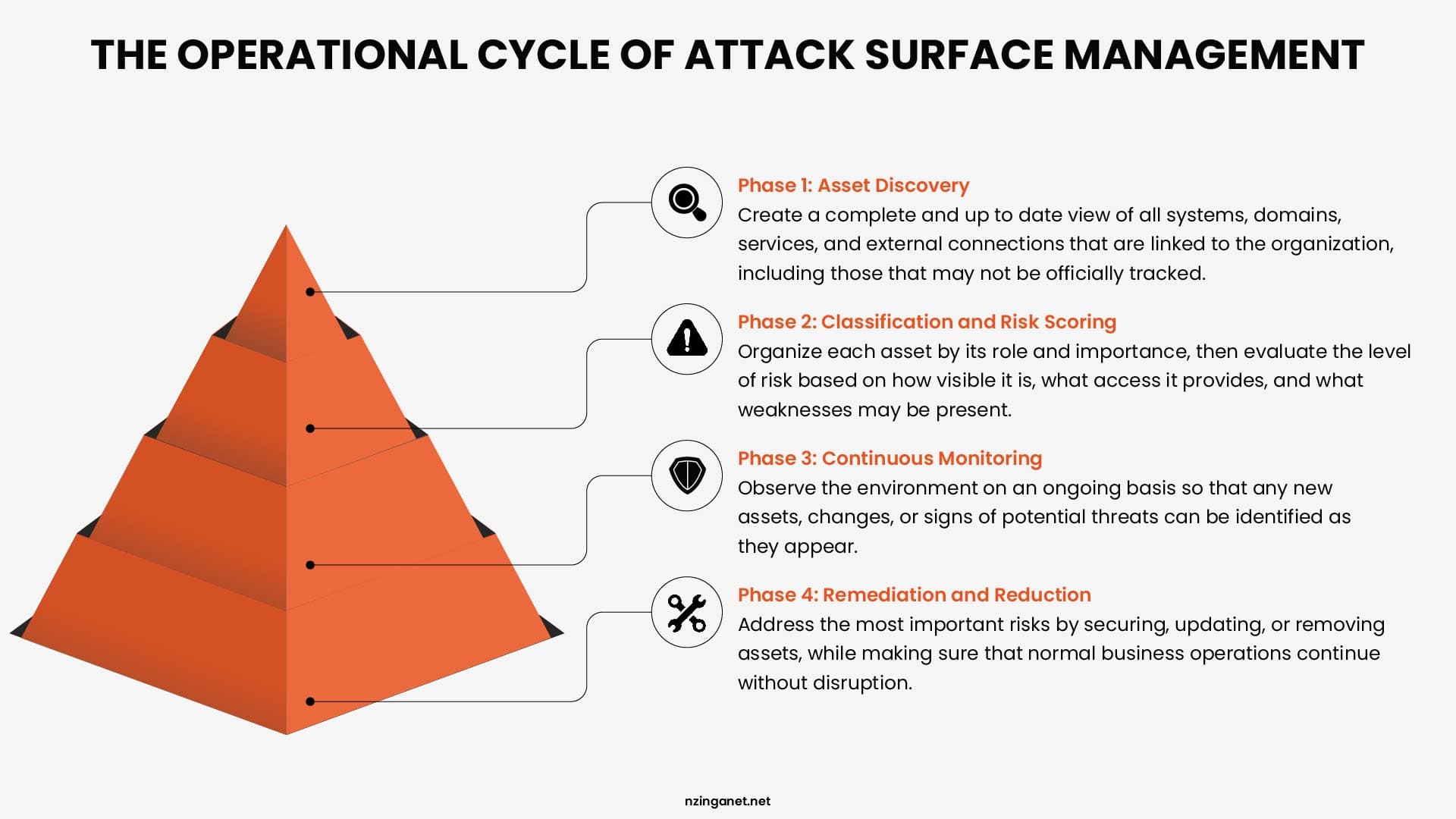
Phase 1: Asset Discovery
Asset discovery is the foundation of every ASM program. The goal is to build a complete, current inventory of every digital asset associated with your organization that is visible or reachable from the outside. This includes assets you have deliberately deployed and assets that exist without your awareness.
Automated discovery tools approach this the way an attacker would: starting with known entry points like the primary domain, and then following connections to uncover subdomains, IP ranges, associated cloud resources, email infrastructure, linked third-party services, and any other asset that bears a connection to the organization.
This outside-in perspective is what distinguishes ASM discovery from a standard internal audit, which cannot see what an attacker sees when they conduct reconnaissance.
Phase 2: Classification and Risk Scoring
Once assets are discovered, they need to be classified by type, purpose, and the sensitivity of the data or access they represent. An internet-facing authentication portal for a healthcare application carries a very different risk profile than an informational subdomain used for a discontinued marketing campaign.
Risk scoring in ASM goes beyond the software vulnerability scores used in standard vulnerability management. It factors in asset discoverability (how easy is it for an attacker to find?), asset criticality (what does a successful compromise give an attacker access to?), and current exposure (what specific weaknesses are present?). This combination produces a prioritized list of the exposures that deserve the most urgent attention.
Phase 3: Continuous Monitoring
An attack surface is never static. Cloud resources are provisioned and deprovisioned. Developers push code with new dependencies. Employees leave and their credentials potentially become available on credential marketplaces. New vendors are onboarded with access to internal systems. Each of these events can change the risk profile of the attack surface.
Continuous monitoring tracks changes in the attack surface in real time, alerting security teams when new assets appear, when existing assets change in ways that introduce new exposure, or when external threat intelligence indicates that an exposed asset is being actively targeted. This replaces the periodic audit model, which could leave an organization unaware of significant new exposures for weeks or months.
Phase 4: Remediation and Reduction
The output of the ASM process is a prioritized action list for reducing the attack surface. This might involve taking down unused subdomains that still resolve to live servers, securing cloud storage that was accidentally configured for public access, rotating credentials that have appeared in data breach datasets, updating software on externally accessible systems, or revoking access for third-party vendors whose project has concluded.
Remediation in ASM is coordinated with the broader security team and with operational stakeholders, because removing or securing an asset sometimes has business implications. The goal is not to eliminate every exposure at any cost but to reduce the attack surface to a level that matches the organization's risk tolerance while maintaining operational capability.
TOOLS
Best Attack Surface Management Tools in 2026
The ASM platform market has matured significantly over the past three years, with both established security vendors adding ASM capabilities to existing suites and purpose-built ASM platforms reaching enterprise-grade maturity. The table below covers the most widely reviewed options across different organizational sizes and use cases.
| Tool | Best For | Key Capabilities | Pricing Model |
|---|---|---|---|
| Palo Alto Cortex Xpanse | Large enterprises | Continuous external discovery, automated remediation | Enterprise, quote-based |
| Microsoft Defender EASM | Microsoft-centric organizations | External asset inventory, exposure monitoring | Included in Microsoft security licensing |
| Tenable.io | Mid-market and enterprise | Asset discovery, vulnerability scanning, exposure analytics | Per asset, subscription model |
| CyCognito | Mid to large enterprise | Automated attacker-perspective reconnaissance | Enterprise, quote-based |
| Bitsight | Global enterprises and regulated industries | Continuous EASM, cyber risk ratings, third-party monitoring | Enterprise, subscription |
| Hadrian | Mid-market organizations | Continuous testing, event-driven asset discovery | Mid-market, quote-based |
| Intruder | SMBs and growing businesses | Automated external scanning, continuous monitoring | From $101/month per target |
SELECTION CRITERIA
What Should You Look for in an ASM Platform?
The right ASM platform depends on the size of your organization, the complexity of your cloud and vendor environment, and the internal capacity you have to act on findings. Regardless of these specifics, the following capabilities should be present in any platform considered for production use.
- Continuous, automated asset discovery: The platform should find assets without requiring manual input of seed data beyond your primary domains.
- Outside-in perspective: The discovery and monitoring should operate from the public internet's viewpoint, finding what an attacker finds.
- Risk-based prioritization: Findings should be scored based on actual exploitability and business impact, not just technical severity.
- Integration with existing security workflows: Findings should be exportable to the ticketing and remediation systems your team already uses.
- Historical change tracking: The platform should maintain a record of how the attack surface has changed over time.
BEST PRACTICES
Attack Surface Management Best Practices
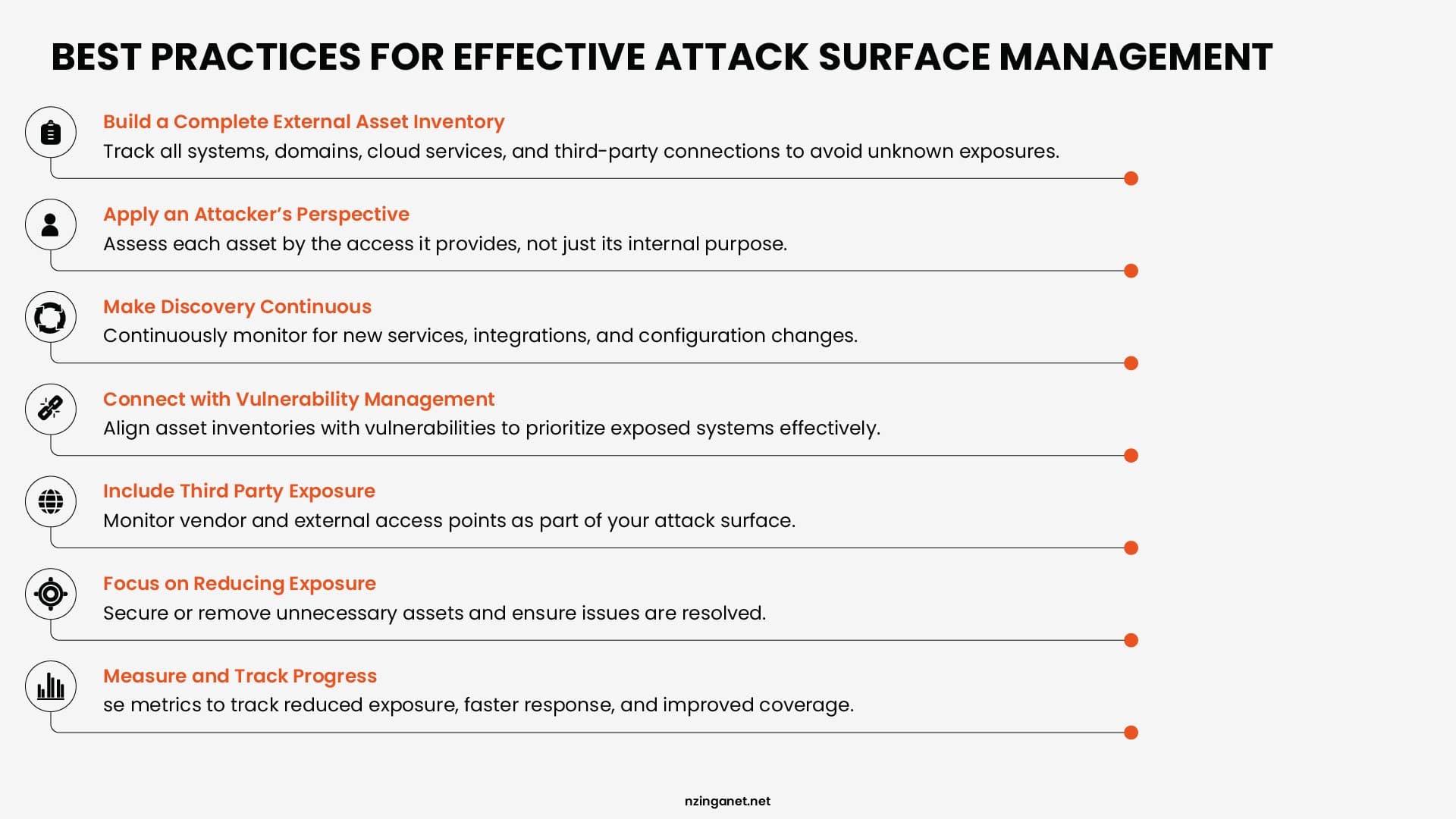
1. Start with a Complete External Asset Inventory
Before addressing risk, you need to know what exists. The first investment in an ASM program should be in asset discovery breadth: ensuring the discovery scope includes all domains and subdomains associated with the organization, all cloud accounts and environments, all acquired entities that may have their own digital footprints, and the primary third-party vendors with access to internal systems.
Most organizations discover more than they expected in this initial inventory phase. Forgotten assets from discontinued projects, infrastructure that was provisioned by a team that has since been restructured, and acquired systems that were never properly integrated into the security monitoring program all appear. The inventory itself, before any remediation begins, is a significant risk reduction step because it eliminates unknown unknowns.
2. Apply the Attacker's Perspective Throughout
ASM works best when it consistently adopts the perspective of an external attacker performing reconnaissance. This means evaluating assets not for their internal importance but for what access they would provide to an attacker who successfully exploited them.
A subdomain that serves only a redirect to the main website might seem low priority internally. From an attacker's perspective, it might represent an opportunity to establish a phishing domain, execute a subdomain takeover, or harvest cookies from users who are redirected improperly. Prioritization that ignores attacker perspective systematically underweights these kinds of exposures.
3. Make Asset Discovery Continuous, Not Periodic
Scheduled quarterly or annual attack surface assessments provide a baseline but leave organizations blind to changes that occur between assessments. New cloud services, new vendor integrations, and new employee digital footprints all introduce exposure that may not be caught until the next scheduled review.
Continuous monitoring should be configured to alert on specific change types that commonly introduce high-priority exposure: new internet-facing services that were not in the previous inventory, certificate changes on authentication systems, new subdomains that resolve to infrastructure not recognized in the asset inventory, and cloud storage resources with public access configurations.
4. Integrate ASM with Vulnerability Management
ASM and vulnerability management are most effective when they share data. The asset inventory that ASM maintains should serve as the input to the vulnerability scanner rather than maintaining two separate inventories. Assets discovered by ASM that are not covered by the vulnerability management program represent blind spots where CVEs can exist without being detected.
The integration should also work in the other direction: vulnerability findings that indicate an asset is running software with an actively exploited vulnerability should trigger elevated urgency in ASM monitoring, ensuring that the exposure is prioritized for immediate remediation rather than placed in a standard remediation queue.
5. Treat Third-Party Exposure as Your Own
Third-party vendors, SaaS platforms, and open-source components are part of your attack surface whether or not they appear in your internal asset inventory. An attacker who compromises a vendor with network access to your environment has effectively compromised your environment. The scope of ASM should explicitly include the primary entry points through which third parties connect to your systems.
This does not require continuous deep monitoring of every vendor's full infrastructure. It requires maintaining visibility into the specific access points through which vendors connect to your systems, monitoring those access points for exposure, and having a process to respond when a vendor reports or you discover a compromise that may have affected your environment.
6. Reduce the Attack Surface Actively, Not Just Monitor It
Monitoring tells you what is exposed. Remediation reduces the exposure. An ASM program that generates findings but has no defined process for acting on them creates documentation of risk without reducing it. Each category of finding should have a defined remediation path: who owns it, what the acceptable remediation timeline is based on severity, and how closure is verified.
Reducing the attack surface also means decommissioning assets that no longer serve a purpose. Unused subdomains, legacy applications still accessible from the internet, and vendor access credentials for integrations that have been discontinued all represent exposure with no offsetting operational value. Retiring these assets is zero-cost risk reduction.
7. Document and Measure Improvement Over Time
Attack surface management is an ongoing program, not a one-time project. Progress should be measured in concrete terms: reduction in the number of unmanaged internet-facing assets, reduction in mean time from asset exposure to remediation, percentage of third-party integrations that have been reviewed and risk-assessed. These metrics demonstrate to leadership that the program is producing results and identify areas where the process needs to improve.
Documented improvement also supports regulatory compliance reporting. Frameworks including NIST CSF, ISO 27001, and PCI-DSS require evidence of continuous security improvement over time. An ASM program with consistent measurement and documentation provides that evidence as a natural output of normal operations.
Moving Forward with ASM
Once you have a clear view of your attack surface, the next step is to act on it. Identify which assets need immediate attention, assign responsibility for each area, and put processes in place to track changes and fix issues as they arise.
Make sure monitoring and remediation are part of daily operations rather than occasional checks. Regularly review progress and adjust priorities based on the most critical risks to your organization.
To get started with a practical, step-by-step plan for managing your attack surface, schedule a consultation with NzingaNet today and let our team guide you through the process.
COMMON QUESTIONS
Frequently Asked Questions
PENNSYLVANIA & BEYOND
Stop Cybersecurity Mistakes Before They Cost You — NzingaNet Can Help
NzingaNet provides managed IT and cybersecurity services to small and mid-sized businesses across Pennsylvania and the surrounding region. From endpoint protection to compliance readiness, we handle the security so you can focus on your business.
| Explore Managed IT Services | Schedule a Free Consultation |



